Zero Trust Security: Core Concepts for Organizations
Zero trust principles, how it differs from perimeter security, key technologies, and a phased adoption roadmap.
Traditional network security works like a castle with a moat. Firewalls keep attackers out, and anyone inside the network is trusted. The problem: once an attacker gets in, they move freely. Compromise one VPN account and the entire internal network is open for exploration.
Zero Trust flips that assumption. Inside or outside, nobody is trusted by default. Every access request is verified, every time.
"Never Trust, Always Verify"
That is the one-line summary. Being on the corporate network does not earn trust. Using a company laptop does not automatically mean safe. Every request gets checked: Who is this user? Is this device secure? Does this user have permission to access this specific resource?
Why did this become necessary?
First, the perimeter disappeared. Post-pandemic remote work is standard. Employees connect from home, coffee shops, airports. "Inside the corporate network means safe" no longer holds.
Second, cloud migration. Data and applications are spread across AWS, Azure, GCP, and SaaS tools. "Internal network" as a concept has dissolved.
Third, attack evolution. The standard pattern is: phish one employee's credentials, then move laterally inside the network, escalating privileges along the way. Perimeter defense alone does not stop this.
Core Principles
Least Privilege
Grant users, devices, and applications only the minimum permissions they need. A marketing team member has no business accessing the production database. Developers do not need admin access to every service.
In AWS IAM terms, "Effect": "Allow", "Action": "*", "Resource": "*" is completely off the table. Scope permissions to the specific services and actions required.
Role-Based Access Control (RBAC) is the baseline. Attribute-Based Access Control (ABAC) goes further by incorporating conditions like time, location, and device state. "Allow access only between 9 AM-6 PM, from a managed device, from an expected geographic region" — that kind of policy becomes possible.
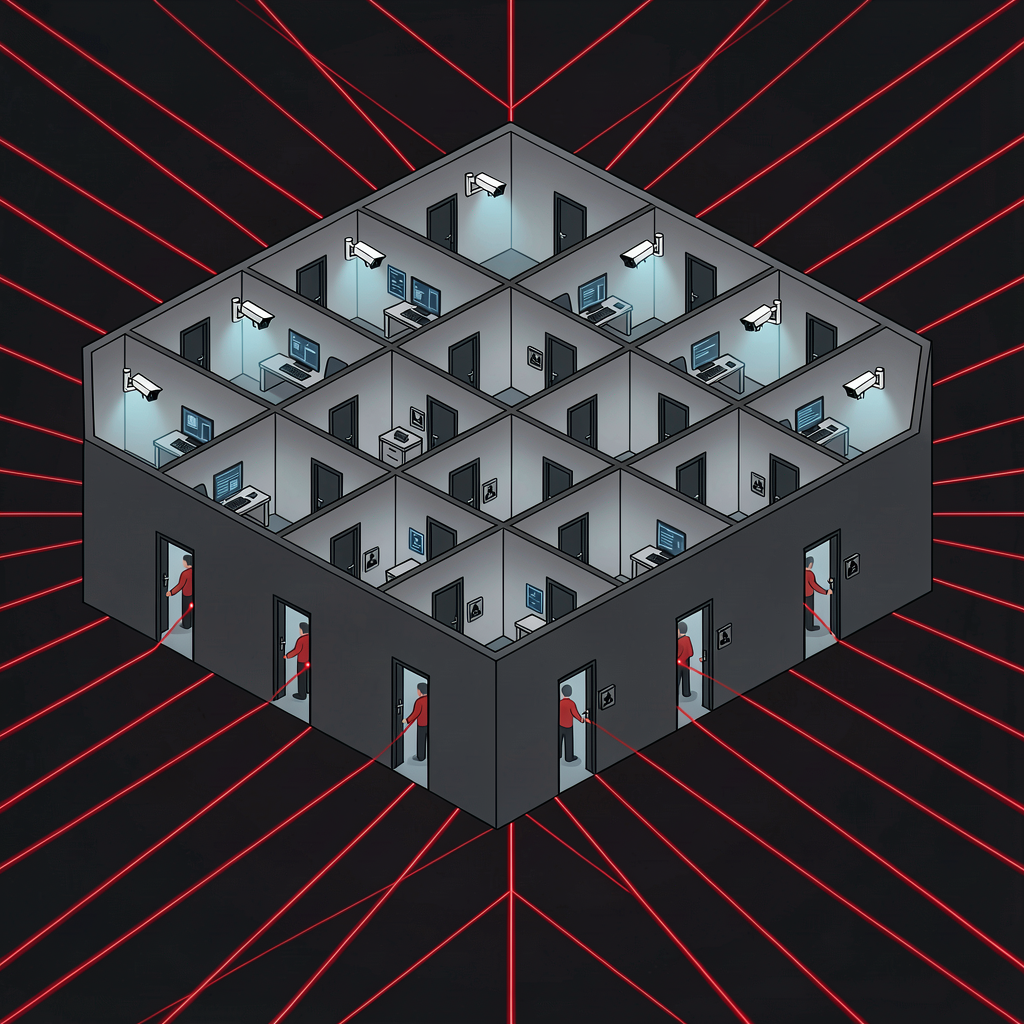
Micro-Segmentation
Divide the network into small zones. Traditional networks let servers on the same VLAN communicate freely. Compromise the web server and the database server on the same segment is one hop away.
Micro-segmentation puts firewalls between individual workloads. The web server can only talk to the app server on a specific port. The app server can only reach the database on a specific port. One compromised component cannot easily reach its neighbors.
In Kubernetes, Network Policies implement this. Pod-to-pod traffic is blocked unless explicitly allowed.
Continuous Verification
Authentication is not a one-time event. Verification continues throughout the session. Sudden login from a different country? Access from a device never used before? Downloading an unusual volume of data? These trigger re-authentication or access revocation.
This approach is sometimes called CARTA — Continuous Adaptive Risk and Trust Assessment. Risk is evaluated in real-time, and access levels adjust dynamically.
Key Technologies
IAM (Identity and Access Management)
The center of zero trust. Confirms user identity, assigns appropriate permissions, controls access.
Beyond passwords, multi-factor authentication (MFA) is baseline. Phishing-resistant authentication — FIDO2 security keys, biometrics — is the recommended standard. SSO (Single Sign-On) centralizes authentication and makes offboarding clean: disable one account and access is cut everywhere.
Major solutions: Okta, Microsoft Entra ID (formerly Azure AD), Google Workspace, Ping Identity.
ZTNA (Zero Trust Network Access)
The VPN replacement. VPN connects you to the whole internal network. ZTNA grants access to specific applications only. The paradigm shifts from "connecting to a network" to "accessing an application."
With VPN, opening the tunnel gives network-level access — you can try reaching any server. ZTNA controls access at the application level, so unauthorized apps are not even visible.
Zscaler Private Access, Cloudflare Access, and Palo Alto Prisma Access are leading ZTNA products.
SDP (Software-Defined Perimeter)
Similar to ZTNA but a broader framework. Before authentication, the service is invisible. DNS lookups fail, port scans return nothing. The service is hidden at the network level until authentication and authorization pass. Only then does the access path open.
Sometimes called a "dark cloud." If it cannot be seen, it cannot be attacked.
EDR / XDR
Endpoint Detection and Response — monitors device security posture and responds to threats. In zero trust, device state factors into trust decisions. An unpatched OS, disabled antivirus, or jailbroken device can trigger access restrictions.
CrowdStrike, SentinelOne, and Microsoft Defender for Endpoint are key players. The trend is moving toward XDR (Extended Detection and Response), which unifies monitoring across endpoints, network, cloud, and email.
Google's BeyondCorp
The most frequently cited large-scale zero trust implementation. Google built this internally starting in 2011.
Core idea: eliminate VPN. Google employees access internal systems the same way whether they are in the office or at home. Every access decision is based on user identity and device state.
BeyondCorp components:
- Device Inventory — tracks every company-managed device and its security status
- Access Proxy — all internal app access goes through a proxy that handles authentication and authorization
- Trust Engine — combines user identity + device state + access policies to determine whether access is granted
Google's BeyondCorp papers (published starting 2014) significantly influenced the broader industry's zero trust movement. Companies like Cloudflare and Zscaler essentially productized this model.
Adoption Roadmap
You cannot switch to zero trust overnight. A phased approach is the only realistic path.
Phase 1: Asset Discovery
Know what you are protecting. Build inventories of users, devices, applications, and data. This is your "Protect Surface" — a focused subset of the broader Attack Surface, identifying the most critical assets.
Phase 2: Map Traffic Flows
Understand who accesses what, from where, and how. You need this picture before you can decide where to place access controls.
Phase 3: Identity-Based Access Controls
Strengthen IAM. Deploy MFA. Implement SSO. Clean up role-based access. Many organizations start here — it offers the best security improvement per unit of effort.
Phase 4: Micro-Segmentation
Segment the network. Start with critical assets and expand gradually.
Phase 5: VPN to ZTNA Migration
Replace VPN with ZTNA. Migrate application by application rather than all at once.
Phase 6: Continuous Monitoring and Improvement
Zero trust is not "deploy and done." It is an ongoing process. Analyze access logs, refine policies, adapt to new threats.
Adoption Challenges
The theory is clean. Reality is messy.
Legacy systems — a 20-year-old on-premises application probably does not support modern authentication protocols. No SAML, no OAuth. Options are: proxy it, or modernize the system entirely.
User experience — constantly demanding authentication creates frustration. MFA fatigue is real. If users are hit with too many prompts, they start approving them mindlessly. The 2022 Uber breach started exactly this way — an attacker with stolen credentials spam-sent MFA push notifications until the employee, tired of the interruptions, approved one.
Balancing security and convenience matters. Adaptive authentication — light friction for low-risk access, heavy verification for high-risk — is the practical answer.
Cost and complexity — zero trust is not a product you buy. It is an architecture spanning IAM, ZTNA, EDR, SIEM, and more. Integrating these is neither cheap nor simple. Small and mid-size companies may find the cost challenging.
Organizational culture — "always verify" can feel like "we don't trust our employees." Before deploying the technology, the entire organization needs to understand why this approach is necessary. A security-team-only initiative rarely succeeds.
Zero Trust Is a Journey, Not a Destination
This is not binary — "we have zero trust" or "we don't." It is a maturity spectrum. Where you sit on that spectrum matters more than whether you have crossed some finish line.
The direction is what counts. From perimeter-based to identity-based security. From implicit trust to explicit verification. From one-time authentication to continuous verification. Move one step at a time. Even just strengthening IAM and deploying MFA meaningfully improves your security posture. Start there and build forward.